-
Welcome to Talking Time's third iteration! If you would like to register for an account, or have already registered but have not yet been confirmed, please read the following:
- The CAPTCHA key's answer is "Percy"
- Once you've completed the registration process please email us from the email you used for registration at percyreghelper@gmail.com and include the username you used for registration
Once you have completed these steps, Moderation Staff will be able to get your account approved.
Hack the planet! Hack the planet! Let's Play Uplink
Back to Let's Play
< 1 2 3 >
< 1 2 3 >
|
#1
|
|||
|
|||
|
Remember the first time you saw Sneakers? Or Hackers? Maybe it was WarGames? Those people could do just about anything with a computer! They made it look cool! They made it look fun!
Quote:
Until now:  Uplink is the fist computer game by Introversion (those cool guys who also brought you Defcon, Darwinia, and Multiwinia) the game is a stylized simulation of hacking. As their wikipedia article describes it: Quote:
Let's go ahead and start the game then, by selecting new user:       What do we want our name to be?  That's been done before...  Wait, that's not me!  Perfect! (our password will be 'pants'  I've never been based in Sydney before, so we'll go with that one!  Oh, hello piracy protection! *Falselogic goes looking for his card* *Falselogic panickly digs through file cabinets and folders for the card...* *Falselogic begins looking on-line for a crack or pdf of the card* *He finds the card in the case where the CD was...*        We probably should just so you guys understand the interface and how all this hacking will go down! Next time! |
|
#2
|
|||
|
|||
|
I tried the demo for this game but had basically no idea what I was doing. It was pretty close to a hacker movie, but probably not my kind of game.
This will be interesting to watch though! |
|
#3
|
|||
|
|||
|
The failure mechanisms in this game are so good, I honestly can't wait until you screw something up.
|
|
#4
|
|||
|
|||
|
Great, now I have to get obsessed with Uplink again for a few days. Thanks a lot flawgic!
|
|
#5
|
|||
|
|||
|
its well worth it. This game is great!
|
|
#6
|
|||
|
|||
|
Awesome! I'm looking forward to seeing how this game works. The Let's Play archive LP was fun enough but not very informative about what's actually happening in terms of gameplay.
|
|
#7
|
|||
|
|||
|
I got this in my Humble Android Bundle and never installed it. Time to play along I guess!
|
|
#8
|
|||
|
|||
|
I'd like to give this game a try but the font is just too dang small. I'm too blind for this game!
|
|
#9
|
|||
|
|||
|
Now that the introduction to the game is complete we know have control of the cursor and can begin entering the seedy and exotic world of blackhat hacking!
We could do that, or we could take the tutorial!             Next is the Finance window (the icon with the dollar sign on it:     Right now we don't have any of the neat stuff described in the software menu all we have is the file_deleter v1.0 and file_copier v1.0     |
|
#10
|
|||
|
|||
          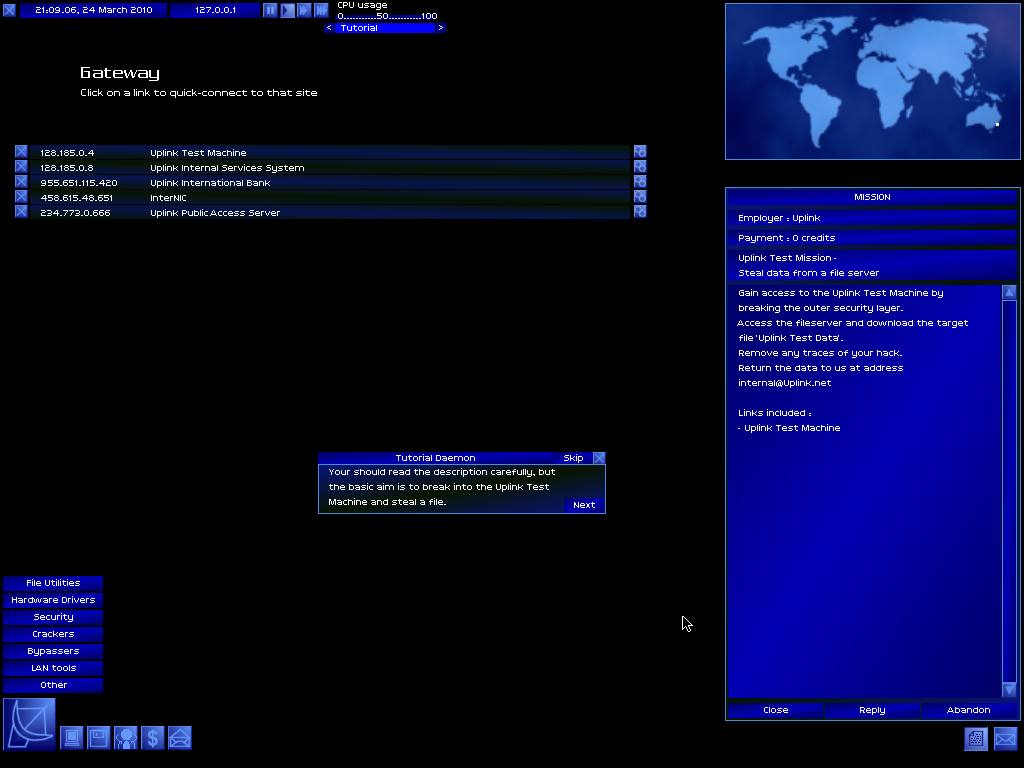  I click on the first bookmark on the lists 'Uplink Test Machine'  Clicking the link will dial us in and connect us to the site. After reading the paragraph we click through:        |
|
#11
|
|||
|
|||
    That is a lot of software! Almost all of it we can't afford nor do we have any idea what any of it is for!  Some people will go for dictionary-hacker but it really is a waste of money because in the end you'll need to purchase password_breaker in the end so best to bite the bullet and pay extra now    We could do that! And if we did we'd be fine... But it is better to learn good habits now rather than have to break bad habits later, so first we hit up:   InterNIC is like the phonebook for the internet in Uplink.  InterNIC is important for two reasons. 1) you'll go here to find sites to hack and/or bounce your call off of, and; 2) Every single job you do the first location you connect to will be InterNIC. Why? Well, because once you get done with the simplest jobs people you have wronged or people whose security you have breached will come looking for you! In order for them not to find you you're going to need to cover your tracks using InterNIC is the easiest way to do that because you can hack it without being found out and so edit their logs with near impunity! I go ahead and add a few sites to my map. You can add all of them all at once but the map becomes unreadable at that point. Once they're added we click on the map and begin bouncing our call around:  Why do this? Once a location realizes its being hacked (usually as you soon as you do something like try to hack the password) it will begin tracing the call. Once it finds out where you are calling from it kills the connection. So the longer your bounce chain is the longer you have to do your hack. Later on we can pick up some software that will tell us how much time we have before we're traced. In order for us to clean up our tracks though we need to break into InterNIC, so we're going to take a break from the Tutorial and break in to InterNIC. We connect to it, click Admin and get this screen:  Click software, and move to crackers and select password_breaker then drag the software onto the password window and let go:  Depending on the speed of your computer and the complexity of the password determines how long it takes to crack the password once it is though:  We're in! What we care about here are the access logs:  See the logs where it says "connection established from 127.0.0.1?" That's us. We're going to want to get rid of this trail as it leads back to our Gateway and that's bad. So we had back to the Uplink Internal Services store and:  The only Log tool we can afford right now is log_deleter. It'll do but we're going to want log_modifier as soon as possible. After we've picked up the log_deleter we reconnect to InterNIC, log-in as the admin, and then select the deleter:    It's not the best answer, as someone can tell the logs have been tampered with and if they have the right software they can find out who, but by the time we start attracting that kind of attention we'll have plenty of money to cover our tracks more thoroughly. |
|
#12
|
|||
|
|||
|
Okay, now that you have a password_cracker and a log_deleter we're ready for the Uplink Test Mission. First we connect to InterNIC and then bounce our signal around a dozen or so sites before connecting to the Test Machine (in general bouncing your call from 12-20 sites is enough to protect you)
 Once at the Test Machine we use the password_breaker to log in (the password was 'rosebud')  Now that we're in we need to 'access fileserver.' Remember the mission is to copy a file from the machine and send it back to Uplink.  'Uplink test data' is the file we're looking for. Open your software select 'file_copier v1.0' and then click onto the file:  Once it's copied we open up our memorybanks and save the file onto our machine:  Once we have the file we can disconnect from the Test Machine, open the email from Uplink, click 'reply'  and then attach the file and send it off:   Shortly after we send the email we get some reply-backs:   With the test mission over, we just have one more tutorial left! Let's start it now:           |
|
#13
|
|||
|
|||
               With the tutorials done, we delete them from our memory banks and then head to InterNIC with our log_deleter. When we're done it looks like this:  Not perfect, but when we log out it'll look like we logged in an 21:15 and then loggeed out about ten minutes later but never left InterNIC. Once we have the right software we'll clean this up too. That's the basics. The hacking jobs get more complicated but you've already got a good idea of what the rest of this game has to offer. Next time we take some real jobs, earn some money, and try to avoid getting caught. |
|
#14
|
|||
|
|||
|
Neuromancer: someone was reading their William Gibson, surely.
(Then I wandered off on a tangent and found out that there was an Interplay computer game based on the novel, complete with 80s adventure game graphics. How surreal.) |
|
#15
|
|||
|
|||
|
I never really got the hang of or particularly enjoyed this game, so I'm looking forward to this LP.
|
|
#16
|
|||
|
|||
|
I have spent far too many hours playing this game over the years. It's one of those unique and interesting games that gets tragically overlooked, and it's great that you're doing an LP for it!
|
|
#17
|
|||
|
|||
|
Welcome back! Sorry it took so long to get this next chapter out. Personal lives, right?
Okay, we've completed the Uplink Test and we've being introduced to the shady world of digital cowboys, server samurais, deckers, hackers, whitehat and blackhats! Let's get out hands dirty! But first let's see where in this world we rank:  Pretty low... Welp, no one starts at the top of the mountain. Okay, not let's hack some computers! Wait, we need to get one more piece of software:  Trace Tracker 1.0, when running, will give us a sense of where the computer systems on the other end are in tracking down where we're intruding from. This is why it's so important always bounce our signal off, at least, a dozen different servers as it gives us some time. V1.0 will sit in the bottom right hand corner and beep. The closer they get to tracking us to our gateway the faster the beeps. More advanced versions will give us a trace percentage, an estimated counter, and even a visual representation of the trace on our map. At just 300c we can easily afford the earliest version. As soon as I get it I got ahead and start it up:  Alright, now we're ready to do some work. Let's check the job board:  The only jobs available to us at first are the easiest. More complicated, and lucrative, jobs will became available as our Uplink ranking increases.  We can't even take these low level jobs at first and have to contact the client:   I try to get him to pay us more and up front but we just don't have enough pull yet, later we can do this. After talking to her though she at least gives us the job:  These low level easy jobs all involve breaking into low security systems and either deleting or copying files. We accept a few:    Our first job is a DELETE FILE job. Our first step is to set up a chain that ends in the target system:  Once we're connected we can stay here forever without triggering a trace. As soon as I run password_breaker and select the log-in screen trace_tracker 1.0 begins pinging:  A few seconds later we're in, we make our way to the file server, check the email and then using file_deleter get rid of it. Client emails always say to delete backups as well but I've never encountered a system that had backups. Or I never noticed it and was never penalized for not delete backups.  Once the file is delete we still have some time (trace_tracker's pinging is a slow beep still) we head into Admin and the Server logs to delete where we connected from and what we did. These logs can be restored but with such a low level crime probably won't be but if they do it will take time. Time enough for us to clean up more thoroughly (FYI you usually have a day to three (in game time) to clean up before tracks.  With some rough shod clean-up work down we disconnect when we do we get this message:  This let's you know that if/when you go back into this particular system you won't be able to use the same password again and will have to re-break it. With the job done we email the client letting him know that the dirty deed is done. A second later we get notification of payment:   And with that our first real job is done. Now let's cover our tracks! Remember how?  That's right. We log back into InterNIC, the password we got the first time will always work here and then scrub the logs. It's messy but soon enough we'll be able to clean it up and make it untraceable. Speaking of traces we should discuss that now. Quote:
 Our bank account doesn't look very big now but that'll be changing sooner than you think! I'm planning something big, REAL big. But before we can pull that off we're going to need some more money. |
|
#18
|
|||
|
|||
|
Our second job is a COPY FILE job:
           With the completion of our second mission we receive an email from Uplink:  A Novice? Woohoo! We've got a couple more of these jobs so I'm just going to show you a montage. Parts of Uplink can be pretty repetitive as you build up the cash you need to get the hardware/software you'll need to do more complicated jobs:        After we do some more of these jobs we begin to see new types of jobs appear on the board:  This next level of jobs involve breaking into government or universities and creating degrees for people or falsifying social security numbers. We'll be tackling these in the next update. |
|
#19
|
|||
|
|||
|
I click for some time to pass and check the news feed:
  You can ignore the News Feed, it's usually full of the fall out from our and other hackers work. This update here though is part of the "storyline" to Uplink and so I wanted to make sure you saw it. Below that is our ranking after just five jobs we've moved up nearly 40 spots! Also, you can see in the bottom right all the jobs I've accepted. Got to make that money. Why do we need that money? For better software:  log_deleter V4.0 is the best form of the deleter software. And I recommend buying it as soon as you can afford it. 4000c is a small price to pay for piece of mind! With V4.0 in our possession we log back into InterNIC and clean it all up:    And that is what it looks like when we're done. When we log out it'll great a log out action that will match up with that only other one that references our Gateway (127.0.0.1) In the future this log will just show or IP logging connecting and then disconnceting. There will be no record of our bounces or of our logging as the Admin. We do some more jobs and level up again:  I also pick up V4.0 of trace_tracker. In the future I'll know just how much time I have for each job before the ACTIVE trace is completed:  Here's our bank balance:  Here is what we'll be doing next time:  In the meantime tell me what you think I should be upgrading our gateway, hardware, software? Keep what we have and just get more money for now? |
|
#20
|
|||
|
|||
|
I think you should spend it on getting drunk and living the high life, so in Act 4 we can see you lose everything and die a lonely, drug addicted, computer hacker.
|
|
#21
|
|||
|
|||
|
If only that were an option. But that AMAZING game has yet to be created...
|
|
#22
|
|||
|
|||
|
I think you should save up for the most ridiculous, over-the-top, unnecessarily powerful hacking software money can buy and show it off.
Assuming there is something like that. |
|
#23
|
|||
|
|||
|
Could you talk more about the mechanics a bit? What are the advantages to upgrading the gateway? What different software might we want to concern ourselves with? What about hardware? I don't know enough about this game to make any decision except "get drunk".
|
|
#24
|
|||
|
|||
|
Quote:
I'll cover upgrades in a mini update. |
|
#25
|
|||
|
|||
|
We don't have enough money for the biggest, baddest machine on the market yet, do we? I'd be inclined to leave it be for now.
|
|
#26
|
|||
|
|||
|
The news thing makes it sounds like 50,000c is a lot, but you're buying software that costs 5000c just three updates into the game. Did it take a lot of time to make that much?
|
|
#27
|
|||
|
|||
|
Mini update coming tonight or tomorrow
Quote:
It took about 20 minutes to make around 15k. The easiest jobs in the game (delete/copy hacks) pay between 1200c and 2000c each jobs takes about two minutes to set up and do and that time could be further reduced through optimization or grouping (have multiple jobs from different people that all target the same server.) Soon enough we'll be pulling off a hack that will end our money worries for the rest of the game. Mid and late game Uplink money becomes less of a resource and more of sign of success. |
|
#28
|
|||
|
|||
|
Credits seem roughly analogous to dollars when it comes to rewards.
|
|
#29
|
|||
|
|||
|
So basically 50,000c is not really much to be throwing around when you're talking about a company that's supposed to be snatching up all the best and brightest.
|
|
#30
|
|||
|
|||
|
There are two broad categories of stuff an Agent can buy in Uplink, Hardware and Software. I'll be introducing the software to everyone as we pick it up. That leaves us with Hardware. Hardware can be broken down into two broad categories as well, Gateways and Devices. Think of Gateways as the case and devices as everything that goes inside them. When you upgrade your Gateway all the devices are transferred to your new one and then can be pulled out when new devices are put in. It's not a perfect comparison as high level gateways can have motion sensors, remote IR access, and self destruct mechanisms in them but it's close enough.
Gateways Gateway Alpha Max CPUs: 1 Max Memory: 32Gq Max Security: 0 Max Bandwidth: 1Gq/s Cost: 5000c The gateway you start the game with, and go back to if your gateway is ever destroyed. It's very simple, with only one CPU slot and 32Gq Max Memory space. There is no room for security, and this model cannot handle a better modem. Gateway Alpha ICPU Max CPUs: 2 Max Memory: 32Gq Max Security: 0 Max Bandwidth: 1Gq/s Cost: 10000c This Gateway is almost exactly the same as the ALPHA, except it has an extra CPU slot, which means it can have double the processor power. Gateway Alpha IMEMORY Max CPUs: 1 Max Memory: 64Gq Max Security: 0 Max Bandwidth: 1gq/s Cost: 10000c This is the same as the ALPHA but with twice as much memory space. The VIRTUANET R-Access Gateway Max CPUs: 2 Max Memory: 48Gq Max Security: 0 Max Bandwidth: 2Gq/s Cost: 17000c This Gateway has 2 CPU slots and enough space for 48Gq of memory, though no space for security. You cannot be caught with this Gateway, (some people have reported being caught with this Gateway) The KRONOS Corp 80-860 Gateway Max CPUs: 2 Max Memory: 64gq Max Security: 1 Max Bandwidth: 4Gq/s Cost: 28000c Has twice the CPU and Memory capacity of the ALPHA, space for a 4Gqs Modem and 1 security device, The ZION-780 Series Workstation Max CPUs: 3 Max Memory: 96Gq Max Security: 2 Max Bandwidth: 6Gq/s Cost: 40000c The ZION has 3 CPU slots, enough space for 96Gq of memory, 2 security devices and a 6Gqs Modem. The UNITY High-Security Platform Max CPUs: 4 Max Memory: 64Gq Max Security: 4 Max Bandwidth: 6Gq/s Cost: 70000c The Unity's main feature is 4 security device spaces, sadly the game only has 2 you can purchase. Having duplicate security devices does nothing to help you. The AM-CORE File Server Max CPUs: 3 Max Memory: 256Gq Max Security: 2 Max Bandwidth: 6Gq/s Cost: 90000c This Gateway's main selling point is the huge amount of memory space. The OMEGA Super Computer Max CPUs: 16 Max Memory: 48Gq Max Security: 1 Max Bandwidth: 4Gq/s Cost: 90000c The fastest possible Gateway in the game with 16 CPU slots. Sadly, lacking in the memory department though. The TRINITY-1686a Gateway Max CPUs: 8 Max Memory: 128Gq Max Security: 3 Max Bandwidth: 8Gq/s Cost: 115000c All around good high end Gateway. 8 CPU slots and 128Gq of Memory space. It does have a superfluous security slot... Devices Devices come in three flavors: Processors, Memory, and Modems Processors The faster the processor the faster your Gateway can do things. Things like crack passwords, decrypt cyphers, disable LANs, etc. 20 Ghz - 250c - Our first Gateway starts with this processor in it. 60 Ghz - 1000c 80 Ghz - 1300c 100 Ghz - 3000c 120 Ghz - 5000c Memory Memory determines how many and what size files you can store on your Gateway. 8 Gq - 3000c - Our Gateway starts with this much memory 16 Gq - 5500c 24 Gq - 8000c 32 Gq - 11000c Modem Determines the speed of file transfers 1 Gq/s - 1000c - the first Gateway comes with this 2 Gq/s - 2000c 4 Gq/s - 4000c 6 Gq/s - 6000c 8 Gq/s - 8000c Misc Gateway Self Destruct - 20000c - Fits specified Gateways with explosives and provides you with software to remotely detonate them Gateway Motion Sensor - 10000c - Attaches a motion sensing device to specified Gateways and provides software to monitor the state of your Gateway. (It's a little light that glows green when all clear, yellow when devices are being installed/replaced, and red when the Authorities show up.) This device is only useful when used in conjunction with the Gateway Self Destruct. Now you know what stuff does what do you think? Do we focus on getting primo devices into our ALPHA gateway first or move to a better Gateway and then upgrade our devices? |
